Identities#
Accounts and identities are strongly linked on the Concordium Platform. To be able to hold, send, or receive CCD or become a validator on the Concordium blockchain, you need an account and an identity. This is regardless of which wallet you use for your transactions.
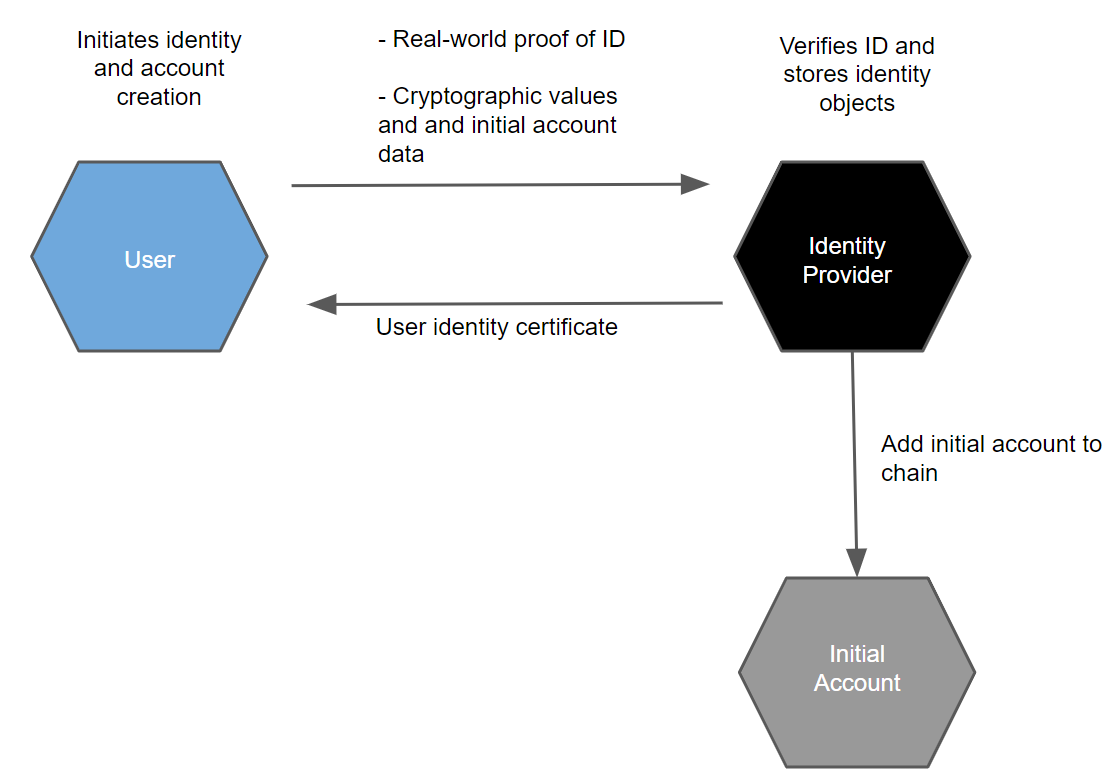
Before you can use the Concordium Platform, an identity provider must verify and record your real-world identity. This identification is performed when you create your first account.
About identities#
Identities are issued by an identity provider. There is a registry of selected identity providers and their contact information publicly accessible from the Concordium blockchain. Concordium Foundation will maintain the list in the beginning.
Note
It is possible to create a company identity that is not associated with a specific individual but is issued with documents that identify a company. Company identities are only relevant for a few companies. The way they are created differs from how individual identities are created. For more information, see Company identity creation.
While identities facilitate compliance with relevant regulations, they also allow users to be represented on-chain in a way that protects users’ privacy. That is, transactions on the chain are processed without exposing the identity of the sender or receiver. The identity of an account owner can only be revealed via the process of disclosing an identity. Disclosing an identity can only happen in exceptional circumstances, for example if authorities have detected suspicious activity on the account, and requires action by one or more identity disclosure authorities and the identity provider who issued the account’s identity.
Every account on the chain must be derived from an identity that is verified and signed by an approved identity provider. It is publicly visible which identity provider issued an identity for an account, and who the identity disclosure authorities are for the account and the identity. In addition to this basic information which enables regulatory compliance, an account owner can choose to publicly reveal other values on their account. These values are called attributes and can be, for example, nationality or country of residence. Publicly accessible attributes enable anybody to check the attributes before interacting with an account. Being able to see who issued the identity enables whoever wishes to interact with an account to judge the level of risk in the transaction. If you choose to reveal attributes, you should have a good reason to do so. The general recommendation is not to reveal attributes.
Attributes#
Each identity contains a number of cryptographic values and a number of user-chosen attributes, such as nationality or country of residence. These attributes are certified by the identity provider. The cryptographic values are a number of public and private keys, a signature from the identity provider, as well as a number of secret values the user must use to be able to use the identity to create accounts.
You are in control of which attributes are revealed to the public. You can choose not to reveal any attributes at all, which is the general recommendation.
Obtain an identity#
You can create identities in the CryptoX Concordium Wallet, Desktop Wallet, Concordium Wallet for Mobile, or Concordium Wallet for Web. Identity creation is an off-chain action.
Warning
It is not possible to exchange identities and accounts between the Concordium Legacy Wallet and the Desktop Wallet. If you try to import a file that has been exported from the Concordium Legacy Wallet into the Desktop Wallet, the import will fail, and likewise, if you try to import a file exported from the Desktop Wallet into the Concordium Legacy Wallet.
Warning
Because of the difference in the way private keys are handled between Concordium Wallet for Mobile / Concordium Wallet for Web and the first generation wallets (Concordium Legacy Wallet and Desktop Wallet), you cannot exchange identities and accounts between them.
It is possible to exchange accounts and identities between the CryptoX Concordium Wallet, Concordium Wallet for Mobile, and the Concordium Wallet for Web. Additionally, Concordium Legacy Wallet users can import backup files to CryptoX Concordium Wallet.
Note
It is no longer possible for users of Concordium Legacy Wallet to create new identities.
Identity issuance requires Identity Verification, which is the process of verifying the real-life identity of the user. This typically requires taking photographs or scans of identification documents, such as a passport. Identity verification also checks that the user-chosen attributes are valid for the user.
Upon verification of the user’s identification documents and attributes, the Identity provider issues a user identity certificate. The User identity certificate contains attributes about the user. It is basically the Identity Provider’s signature over some cryptographic keys of the user and the validated personal attributes.
Note
If using CryptoX Concordium Wallet, Concordium Wallet for Web, or Concordium Wallet for Mobile with Digitial Trust Solutions (DTS) as your identity provider, and you have a mitID (Denmark) or Suomi.fi e-identification (Finland), you can use that to complete the identity verification process.
About accounts#
For information about accounts, see Accounts.
Note
It is no longer possible for users of Concordium Legacy Wallet to create new accounts.
Disclosing an identity#
The identity of a user can only be disclosed to a qualified authority as part of a valid legal process. A qualified authority is a governmental body that has authority to act in a relevant jurisdiction. For example, a local police force, a local court or an investigatory division of a local authority that regulates financial conduct will all have authority to act in their jurisdictions. These authorities are qualified to begin the process of disclosing the identity of a user when they proceed through established legal channels and make a formal request. The outcome of such a request is likely to be that a qualified authority obtains an official order, which may be in the form of a warrant, court order, or similar instrument. Only after a qualified authority validly serves an official order upon the relevant identity disclosure authorities and identity provider can the real-world identity of a user be revealed and only to the extent set out in the order.
When legally obliged, the identity disclosure authorities and identity provider work together to determine the owner of an account and determine which accounts belong to the same owner. Disclosing an identity is a multi-stage process requiring cooperation of multiple parties.
Each account has an encryption of a specific user identifier. This number can be decrypted by a sufficient number of identity disclosure authorities working together. The set of identity disclosure authorities and the number of them required to decrypt the user identifier are determined when the identity is issued.
After the authorities have identified an on-chain transaction or account they would like to investigate, in order to reveal the real-world identity of a user, the following process must be followed:
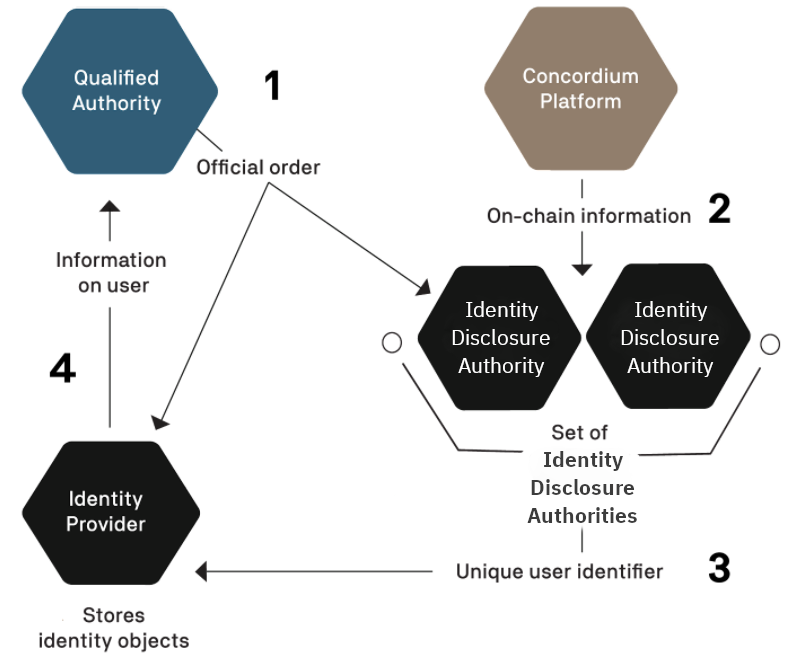
The qualified authority must identify the identity disclosure authorities and identity provider associated with the account they would like to reveal and present them with an official order.
Per the terms of the official order, the identity disclosure authorities inspect and decrypt the available on-chain data for the user.
The identity disclosure authorities extract the unique user identifier from the collected data.
With this unique user identifier, the qualified authority can work with the relevant identity provider to retrieve the real-world identity of the user. The identity disclosure authorities can also decrypt a value that is held by the identity provider to find all accounts the user has created from a given identity. Additionally, this value allows identity disclosure authorities to see the amount of CCDs in the shielded balance (deprecated) of the revealed accounts.
All of these actions are subject to rules and processes, and only the relevant entities learn any information about the account owner. No information is publicly revealed.
